Severity
High
Analysis Summary
StripedFly is a sophisticated cross-platform malware framework that has evaded detection for about five years from cybersecurity researchers and infected more than a million Windows and Linux systems since then.
The researchers uncovered the malicious framework last year and found evidence that it started its activities as far back as 2017, and the malware was wrongly recognized as just being a Monero cryptocurrency miner. They describe StripedFly as an advance malware that comes with a variety of features, like sophisticated TOR-based traffic that can hide its mechanisms, worm-like spreading capabilities, automatically updating from trusted platforms, and a custom EternalBlue SMBv1 exploit that was created before the flaw was publicly disclosed.
It’s currently not clear that if this framework was used for generating revenue or cyber espionage, but the researchers say that such an advanced malware indicates that it is probably deployed by an advanced persistent threat (APT) group. Looking at the compiler timestamp for the malware, the earliest known version of StripedFly that featured EternalBlue was back in April 2016.
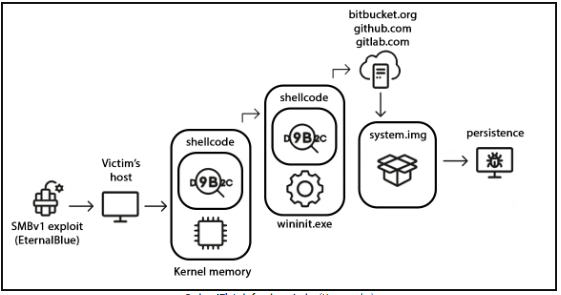
This malware was first discovered after cybersecurity researchers found its shellcode injected into the WININIT.EXE process, which is a legitimate Windows operating system process responsible for handling the initialization of many different subsystems.
After some investigation, they found that it downloads and executes additional files like PowerShell scripts that are from legitimate hosting services like GitHub, Bitbucket, and GitLab. It came to light that the internet-exposed compromised devices were first breached using a custom EternalBlue SMBv1 exploit.
The final payload of StripedFly is called system.img and it features a TOR network client that is custom and lightweight, which is able to protect its network communications from being interrupted. It is also capable of disabling the SMBv1 protocol and spread to other Windows and Linux systems present on the network using EternalBlue and SSH.
The TOR network also contains the malware’s command and control (C2) server, and they’re able to communicate together using frequent beacon messages that contain the victim’s unique ID.
To develop persistence on systems with Windows, StripedFly can adjust its behavior according to the level of privileges it has and the presence of PowerShell. If there is no PowerShell, then it creates a hidden file in the %APPDATA% directory. When PowerShell is available, it instead executes scripts that can create scheduled tasks or modify Windows Registry keys.
Meanwhile on Linux, the malware takes the name ‘sd-pam’. It is able to achieve persistence using either a .desktop file that can auto-start, systemd services, or by modifying different profile and startup files like /etc/rc*, profile, bashrc, or inittab files.
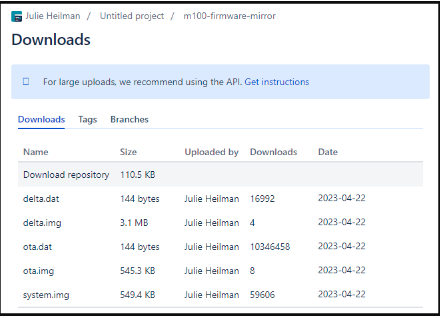
The Bitbucket repository delivers the final stage payload on Windows systems, and it shows that there have been almost 60,000 systems compromised between April 2023 and September 2023. It is also estimated that since February 2022, StripedFly has infected at least 220,000 Windows systems, but there are no statistics available before that date despite the repository being created in 2018. The researchers estimate that over a million devices were infected by the StripedFly framework.
The StripedFly malware framework operates as a monolithic binary executable with modules that can be plugged, which makes it versatile in its operations and makes them similar to APT operations. Following are the modules that StripedFly uses:
- Configuration storage: Stores encrypted malware configuration.
- Upgrade/Uninstall: Manages updates or removal based on C2 server commands.
- Reverse proxy: Allows remote actions on the victim’s network.
- Miscellaneous command handler: Executes varied commands like screenshot capture and shellcode execution.
- Credential harvester: Scans and collects sensitive user data like passwords and usernames.
- Repeatable tasks: Carries out specific tasks under certain conditions, such as microphone recording.
- Recon module: Sends detailed system information to the C2 server.
- SSH infector: Uses harvested SSH credentials to penetrate other systems.
- SMBv1 infector: Worms into other Windows systems using a custom EternalBlue exploit.
- Monero mining module: Mines Monero while camouflaged as a “chrome.exe” process.
Monero cryptocurrency miner is used as a way to create diversion, and the primary objectives of the threat actors is stealing data and exploiting the infected system with the help of the other modules.
“The malware payload encompasses multiple modules, enabling the actor to perform as an APT, as a crypto miner, and even as a ransomware group,” reads the report published by the security experts.
The researchers also emphasize on the fact that the mining module seems to be the primary factor that enables the malware to avoid getting detected for long periods of time. They also found links to the ransomware variant of ThunderCrypt that is able to utilize the same C2 server.
Impact
- Sensitive Data Theft
- Cyber Espionage
- Credential Theft
- Financial Loss
Indicators of Compromise
IP
- 5.255.86.125
- 45.9.148.21
- 45.9.148.36
- 45.9.148.132
MD5
- 54dd5c70f67df5dc8d750f19ececd797
- c04868dabd6b9ce132a790fdc02acc14
SHA-256
- 4456ea66d1fc349fff139305e6d0939ea101b0f0b149d0108a09d007fa2b611a
- 3d90049714406292f10b21b9ccd11bf2a264396ac710e42518138e23c632e5f6
SHA-1
- de8e1785d227914d915ab1d69736b2fdd3fcc3df
- 8b6c6fd39b298ac109da1eadf25b62a93bd99012
URL
- https://bitbucket.org/JulieHeilman/m100-firmware-mirror/downloads/
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Ensure that all systems, software, and applications are up-to-date with the latest security patches. Regularly check for and apply updates to eliminate known vulnerabilities that attackers could exploit.
- Educate employees about phishing emails, social engineering tactics, and safe online behavior. Effective training can reduce the likelihood of users inadvertently initiating an attack.
- Regularly back up critical data and systems to offline or isolated storage. Test the backup restoration process to ensure that it is effective in case of an attack.
- Deploy strong endpoint protection solutions that include advanced threat detection, behavior monitoring, and real-time protection against malware and ransomware.
- Employ robust email filtering and anti-phishing solutions to detect and prevent malicious attachments and links from reaching user inboxes.
- Conduct regular penetration testing and security assessments to identify vulnerabilities and weaknesses in your network and systems. Address any findings promptly.
- Thoroughly assess third-party vendors and software before integrating them into your environment. Ensure they have strong security practices and adhere to cybersecurity standards.

