Earlier this week, the sole electric power supply company of Karachi, Pakistan, was hit by a ransomware attack that affected their online services and billing processes. In response, the company isolated a few services.
“While all critical customer services including bill payment solutions and 118 call centre are operational and fully functional to ensure the integrity of our systems, as a precautionary measure, we have isolated a few non-critical services,” said a KE spokesperson on Wednesday.
Researchers upon further digging found out that the ransomware associated with this attack was NetWalker (aka Mailto, Kazkavkovkiz, Kokoklock, KoKo). Security researchers first discovered the ransomware in August 2019.
Impact on the Organization
K-Electric is the largest power supplier in Pakistan that reportedly serves around 2.5 million customers, and employs more than ten thousand people in the largest city, Karachi. The ransomware attack hit the firm early morning of 7th September, after which the K-Electric customers faced an inability to access the online services for their accounts. Apart from suspension of these online services, no affect was observed on the supplier’s operational workflow and power supply to the city was not interrupted. However, the attackers aren’t likely to take a break anytime soon, as within the same week NetWalker has also hit the data center colocation giant Equinix, on Thursday, and demanded a $4.5 million ransom to prevent the release of stolen data.
NetWalker Ransomware; Brief Overview
First discovered in August 2019, NetWalker was initially called Mailto ransomware because it appended this extension to the files that it encrypted. It was later discovered through the analysis of one of its decryptors that the ransomware is called NetWalker. The ransomware is capable of compromising enterprise networks and encrypting the Windows devices connected to a compromised network. Its payload contains an embedded configuration which upon execution includes ransom notes and files along with other configuration options. So far, it has been evaluated that the NetWalker ransomware first originated from Russia, having been created by a Russian-speaking group of hackers.
Motivation Behind NetWalker Infections
Since Ransomware was created to acquire a ransom payment from the compromised networks, it can be said that the motivation behind NetWalker infections is financial gain. Recently, most ransomware have been going overboard with this financial motivation and have been exposing confidential data of victims online when they fail to acquire the ransom payment.
Attack Vectors
One common attack vector used by the NetWalker operators is that of phishing emails. Their phishing emails use Coronavirus themed malicious attachments containing a VBS script that executes the payload of the ransomware, when opened. The concerning part about the ransomware spreading via VBScripts is that if successful, it may infect all the machines connected to the same Windows network as the original infection point. Another vector is an executable file that has been spread on the network. Without relevant security controls, execution of the file may lead to a compromise.
NetWalker as RAAS
NetWalker Ransomware, the malicious tool that affected K-Electric’s online services, is a tool sold as a Ransomware-As-A-Service program in underground forums by an actor “Bugatti,” who is making efforts to recruit other actors for diversification of NetWalker’s distribution methods. The actor aims to include targeted network attacks and diverse spam operations in its attack practices. One peculiar characteristic about this ransomware’s operators is that they do not accept English-speaking partners. In addition, they forbid their partners from targeting entities based in the Commonwealth of Independent States (CIS). Moreover, majority of organizations purportedly impacted by NetWalker are based in the United States and span across nearly every industry sector, including healthcare, government, professional services, financial services, education, and technology.
NetWalker’s Affiliate Programs
Their advertisements on a popular Russian-language forum exploit.in from March 19, 2020 reveal that the actor is looking for potential partners having persistent access to valuable networks with demonstrated ability of successful network intrusions. In order to lure competent partners, they offer different revenue-sharing options as well. They offer different percentages of revenues to affiliates depending on the total amount generated by the ransomware attacks. From what their advertisement posts reveal, the operators are offering following profit percentages to partners:
- 90/10 percent share of profits when over $200,000 USD are generated per week
- 85/15 percent share of profits when amounts between $100,000–$200,000 USD are generated per week
- 80/20 percent share for revenues less than $100,000 USD a week
Not just higher revenues, Bugatti is also offering increased access to NetWalker’s encryption methods to affiliates having the ability to conduct profitable operations. This shows that the ransomware operators aren’t likely to stop any time soon. In fact, they are offering to provide unlimited access to the EXE auto-crypter and a file-less NetWalker loader written in PowerShell, whenever an affiliate successfully generates at least 10 Bitcoins (approximately $94,000 USD). Apart from these offers, Bugatti also tends to attract less experienced cybercriminals by offering “contractual work” for affiliates who can “prove themselves”. Moreover, Bugatti is offering its partners access to an administrative panel to be accessed over TOR. Comprised of four primary sections, Statistics, Builds, Service and Settings, this panel lets clients manage their encryption keys, NetWalker builds, and payments.
Ransom Payments and Victim-Shaming
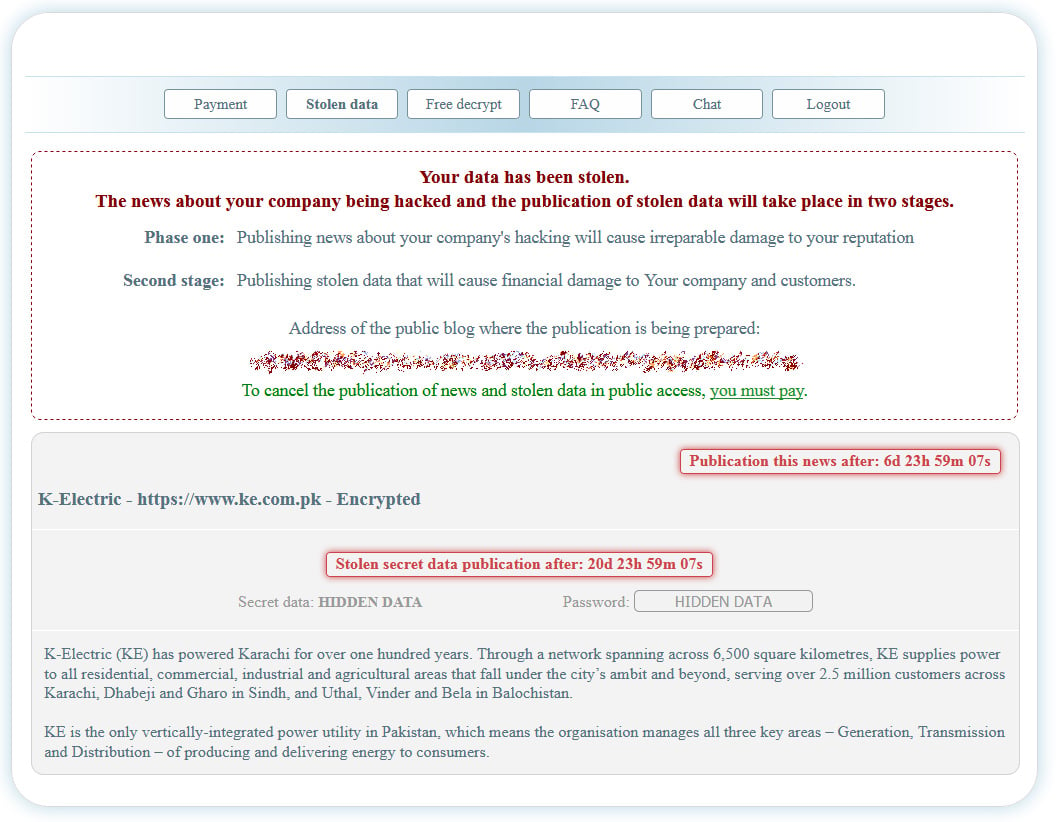
The actors operating NetWalker follow the trail of victim-shaming employed by many ransomware operators recently. This means that when a compromised victim fails to pay a ransom amount, their confidential data will be posted online, causing a major confidentiality breach. Hence, victims’ data stolen from NetWalker operations was found exposed online via a public-facing website, since May 2020. On a TOR payment page, it was observed that the ransomware operators demand a $3,850,000 ransom payment. If a ransom is not paid within another seven days, the ransom will increase to $7.7 million. The ransom note from the TOR payment page is attached below.

Apart from the ransom note, the Tor payment site also has a ‘Stolen data’ page which indicates that the NetWalker operator has also stolen unencrypted files from the victim organization before performing this attack. However, information on the amount of stolen data is not yet available.
Attack Tools
It is suspected that NetWalker operators perform exploitation of vulnerabilities to intrude a target network.
- The Telerik vulnerability CVE-2019-18935 (a deserialization vulnerability that can enable remote code execution in some versions of the Progress Telerik UI for ASP.NET AJAX) is being used for initial entry into victim environments. This is suspected because in multiple incidents that exploited the same vulnerability in April and May 2020, NetWalker Ransomware was later deployed in the victim network. During analysis of compromised systems, security experts have also found evidence of open-source and commercially available attack tools post compromise.
- Another remote code execution vulnerability (CVE-2020-0796) is being exploited that exists in the way that the Microsoft Server Message Block 3.1.1 (SMBv3) protocol handles certain requests. An attacker who successfully exploited the vulnerability could gain the ability to execute code on the target server or client.
- NetWalker operators also exploit the Pulse Secure VPN vulnerability (CVE-2019-11510) that has continuously been exploited by threat actors.
- Apart from newly discovered vulnerabilities, NetWalker operators are also exploiting two of the very old privilege escalation vulnerabilities in Microsoft Windows server, i.e, CVE-2017-0213 and CVE-2015-1701.
- NetWalker campaigns are also found exploiting a Windows zero-day that was earlier exploited in the wild as well.
- As the earlier NetWalker campaigns appeared to rely on phishing messages and password spray attacks, the recent Telerik server exploitations indicate that at least one NetWalker ransomware affiliate has introduced this new intrusion vector.
Moreover, NetWalker operators also use the following tools during the attack.
- LaZagne
- Mimikatz
- NetWalker
- NL Brute
- PsExec
- pwdump
- SoftPerfect Network Scanner
- TeamViewer
- Windows Credential Editor
Victimology
NetWalker incidents have been observed affecting organizations across multiple continents in Australia, Canada, the UK, and the U.S. NetWalker operators were found targeting organizations from almost every sector including healthcare, government, education, financial services, and manufacturing. Recently, in April and May 2020, five educational institutions in the USA were allegedly compromised whereas five healthcare organizations have been impacted by NetWalker since March, 2020.
NetWalker IoCs
Find the latest IoCs Here and Here.
Remediation
- Spread maximum awareness about phishing emails within your organization.
- Organizations should have signatures deployed in their IDS/IPS or EDR against these tools.
- Block the IoCs related to NetWalker ransomware.
- Maintain vulnerability management program, so all vulnerable products can be timely patched as soon as an update is available.
- It is highly recommended to make periodic backups of files and to store them isolated from the network.
- Keep an updated antivirus solution running on all devices.
- As RDP has been observed as a common attack vector for ransomware, it is also crucial to avoid unnecessary Remote Desktop Connections.
- Only use authentic and reputed file sharing services.
- Always download software from official sources and strictly avoid using pirated software.
- Users should disable macros for office programs and must not enable them unless it is essential to do so.
- Some attacks can still be launched through read-only files without enabling of macros, therefore awareness against malspam should be the first line of defense.

